Dutch researchers publish Mifare hack
07 October, 2008
category: Contactless, Transit
Hackers from the Dutch Radboud University Nijmegen gave a presentation on how to break the encryption with some older contactless smart cards, according to a news report on InfoWorld.com. The researchers presented their findings during the Esorics security conference in Malaga, Spain.
In a paper released detailing the research, the hackers say they discovered the workings of the chip by analyzing communication between the chip and the reader and found out the cryptographic protocol. They also used previously released research of similar encryption hacks.
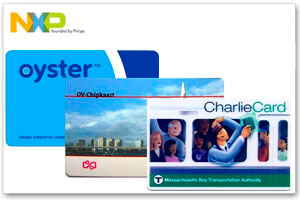
The MIFARE Classic line, the line the hackers broke, includes the MIFARE 1K, MIFARE 4K and MIFARE Mini products. They are used worldwide in transit fare collection systems, access control solutions, and government ID systems. Large issuers include transit projects such as London’s Oyster program, The Netherlands’ OV-chipkaart, and Boston’s Charlie Card.
NXP sued the hackers in July to prevent the research from being released. NXP argued that the research would irresponsibly expose the MIFARE Classic to hacking, adversely affecting public transit and other systems using the chip. The researchers responded that NXP has been allowed ample time to fix the problems, pointing out that clones of the chip have been available since 2004, thus indicating a public knowledge of its inner workings for at least that long.
A Dutch court rejected NXP’s request to prevent the publication of the study of ruling that freedom of speech outweighs NXP’s commercial interests. The judge argued that freedom of speech applies to scientific research as well as individuals.
See our previous coverage of the Mifare Classic hack here.