OpenID launches self-certification testing, trust framework registry
22 April, 2015
category: Corporate, Digital ID, Financial, Government
The importance of standards is well established. Making sure systems and components from different manufacturers work together is essential.
In the identity world there are long-established standards but they haven’t been without their share of problems. On one side, you have programmers slightly tinkering with the specifications, which impacts interoperability. And on the other side, you have products and systems that can be submitted to third-party test labs for certification – a process that is timely and expensive.
Now, the OpenID Foundation wants to enable easy interoperability of OpenID Connect and has announced a self-certification program for the standard that ensures that those deploying it are adhering to the spec, says Don Thibeau, president and chairman of the Open Identity Exchange. The Open Identity Exchange also launched OIXnet, an online registry of trust frameworks and identity systems. It is a registry developed by global leaders across industry sectors to enable online transactions at higher volumes, velocity and variety.
More than six-years ago, Mike Jones, a standards architect at Microsoft, convinced the computing giant to participate in SAML certification with the Liberty Alliance – now the Kantara Initiative. The company has a product coming out that was using the spec and he told executives it would be a good thing from an engineering perspective. “We can also ensure that our products will work, instead of having customer go through and sort out little problems,” he adds.
Now SAML is viewed as being too difficult to work with and over the years programmers have made changes so that different implementations are not longer interoperable. OpenID Connect has built support for modern web developers using the latest data structures, Jones says.
Even before OpenID Connect was officially ratified more than a year ago, there were server interoperability tests that made sure one implementation worked with another, Jones explains. “We would get a dozen different implementations and see if we can talk to one another and do certain things,” he adds.
Coinciding with these interoperability tests Umea University in Sweden was awarded a grant from the GEANT Project, a European research and education institution, to support interoperable identities, Jones says. The university took some of the grant money and built software to test OpenID Connect implementations and features.
Between the interoperability tests and the project in Europe the OpenID Foundation decided they wanted to add some “teeth” to the testing, Jones says. The foundation came up with funding to pay UMEA to adapt the interoperability test software and create a formal certification program. “People would participate in parts of the test they wanted to, but there wasn’t a sense that people would get complete coverage of the specification,” he explains.
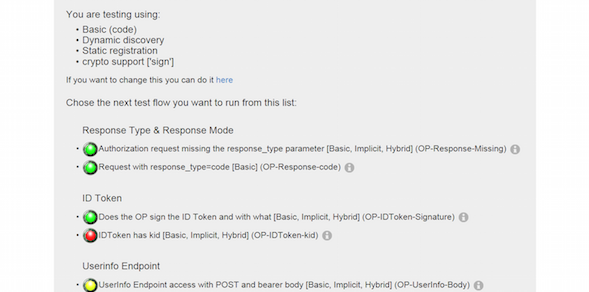
The test is up and running and enables vendors to load the code and run it against the protocol. The dashboard gives feedback in the form of red, yellow and green lights. Once a system runs with all green lights the vendor signs a legal attestation saying they are compliant. The legal agreement, along with all the testing details, are bundled and put on the site for all to review.
“The whole mantra has been to keep things simple by letting people run their own test,” Jones explains. “This is different from the SAML tests wherein the Liberty Alliance participants had to pay a five-figure amount to a third party to run the test.”
Google, Microsoft, ForgeRock, Ping Identity, Nomura Research Institute and PayPal are the first industry leaders to participate in the OpenID Connect Certification program and certify that their implementations conform to one or more of the profiles of the OpenID Connect standard.
“Interoperability between systems is what you need to support a vibrant identity ecosystem,” says Eve Maler, vice president of innovation and emerging technology at ForgeRock. “Identity relationship management relies on portable, secure identities and this means different systems need to talk to one another.”