Analysis: Biometrics and the iPhone
16 September, 2013
category: Biometrics, Digital ID
The inclusion of a fingerprint scanner on Apple’s latest iPhone was one of the worst kept secrets leading up to the device’s September launch event. Rumors had been circulating on gadget blogs for months about the possible biometric inclusion.
So to affirm what the world already knew, the computing giant made the iPhone’s biometric utility official, and while Apple might not be the first handset manufacturer to include a fingerprint scanner, it could well make the biggest impact.
The facts
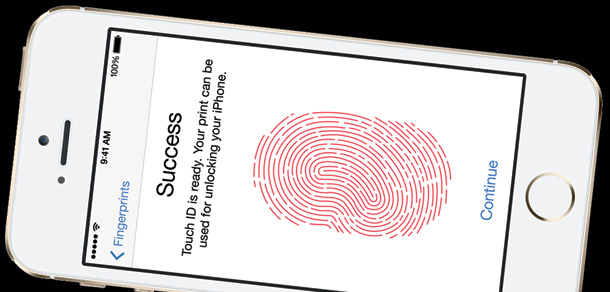
Rather than inputting a numerical PIN, the new iPhone 5S enables users to simply place their finger on the home button to wake the device. In addition to activating the device, the fingerprint sensor will also be used to approve purchases on the iTunes, App and iBooks Stores, eliminating the need to enter a password.
Touch ID supports 360-degree fingerprint readability, meaning the orientation of the applied fingerprint doesn’t matter. The system also enables the iPhone’s owner to enroll multiple fingerprints, enabling the enrollment of other, trusted individuals.
The fingerprint template is stored on a secure element on the iPhone itself, never leaving the device. The fingerprint scanner is optional in that users can opt for a PIN or forgo any additional security features to wake the device if they so choose.
Reaction
A common tweet after the announcement was that Apple was going to be sending fingerprint data to the National Security Agency. This was alluding to the notion that Apple had tapped into iPhone and shared user data with the NSA.
Fingerprint limited to App store
Apple’s iPhone 5S fingerprint announcement is certainly an important development for the biometrics industry. One downside, however, is that the scanner can only be used for access to the device or to confirm purchases in Apple’s App Store.
Opening up the Touch ID application programming interface to other apps would make it possible for secure login to banking, social networking and other apps. This also could be done in a privacy enhancing way so that the other apps don’t have access to the user’s actual fingerprint image.
“It would be fantastic if Apple would enable third parties to utilize the sensor as a second factor of authentication,” says Richard Henderson, security strategist and threat researcher for Fortinet’s FortiGuard Labs. “Want to use your company’s VPN? Please enter your password and place your finger on the sensor. The additional security to mobile apps like banking, Facebook, Twitter and the like would be a no-brainer as well.”
Apple declined to comment on whether the API for Touch ID would be made available.
There was also a common concern regarding fingerprint biometrics and the criminal stigma associated with the modality. While Apple stated that the fingerprint would be encrypted and stored on the device, never leaving, that didn’t necessarily get across to people listening who had fears of network attacks on the devices leading to compromised fingerprint images.
“People don’t understand how this technology works,” says Phillip Dunkelberger, CEO at Nok Nok Labs. “The scanner doesn’t take a picture, it essentially maps it, encrypts and then encrypts it again in the hardware, making it difficult to come back and be a picture.”
Consumers need to be educated on how these systems work so they understand how they can improve privacy, Dunkelberger says.
The gummy finger has also been brought up as security vulnerability. More than a decade ago Japanese researchers were able to replicate fingerprints and use them to spoof fingerprint scanners.
While some fingerprint scanners are designed to test liveness this is still a vulnerability of many readers. The exact details and specifications of Apple’s scanners weren’t released, but AuthenTec – the biometric company Apple bought and whose technology is likely being used to power the scanner – did have some anti-spoofing technology in place, says Walter Hamilton, senior consultant at Identification Technology Partners and vice chair of the International Biometrics & Identification Association.
“AuthenTec had implemented some fake finger counter measures in their commercial fingerprint sensor products some time ago,” Hamilton explains. “They measured the electric field emitted by living human skin so that a plastic or other inert material or prosthetic finger molded from someone’s fingerprint lifted from a glass wouldn’t work.”
That said, no security system is foolproof and because of the high-profile nature of the iPhone 5S, it’s likely to be spoofed pretty quickly after release, says Bryan Ichikawa, senior manager in Enterprise Risk Services at Deloitte and Touche. Lifting a latent print and recreating a finger can be difficult but using it to fool a device is not.
“If you’re going through a security checkpoint with a guard and trying to use a fake finger it’s obvious,” Ichikawa explains. “But if you’re using it to access a device it’s easy.”
As soon as the device is released someone is going to try and spoof the scanner, it’s a matter of when, not if, Ichikawa explains. He wonders what response Apple will have when YouTube videos start appearing showing the scanner being spoofed. “I’m worried this is going to give biometrics a black eye.”
The old adage when it comes to security technology is that with enough time and money any system can be hacked, an idea that applies to Touch ID as well. “No security system is ever 100% foolproof,” Hamilton says. “To be more realistic, you might want to phrase the question another way: Is the fingerprint sensor more secure than a simple password? I think that the answer to that question is a resounding yes.”
PINs and passwords are easy to exploit and can be acquired by social networking attacks, shoulder surfing or a number of other methods. In order to compromise a biometric sensor, the data has to be retrieved, replicated and then entered, none of which are as simple as entering a user name and password. “This is much more difficult than entering a stolen PIN or password and assumes that the sensor has no liveness detection countermeasure capability,” Hamilton adds.
There is also the user convenience factor, swiping a finger on a mobile device is easier than typing in a complex password. “Most enhancements in security features – complex passwords or multi-factor challenge/response – carry significant negative impacts to user convenience and users will simply avoid using them if possible,” Hamilton says.