Biometrics are good, biometrics are bad … good, bad … good, bad…
25 August, 2016
category: Biometrics, Corporate, Digital ID
The lovely month of August; typically one of the hotter months of the year, a time of vacation before kids go back to school and a period of dread for journalists as they try to scrap up enough content to update the web site daily.
Since it’s a slow news month the same stories seem to get played over and over again. There have been two themes when it comes to authentication technology this month: people want passwords over biometrics and <gasp> some researchers found vulnerability with facial recognition biometrics.
The survey is interesting because it shows that the industry has a ways to go to educate consumers on how biometric technology works. It states that 42% of consumers do not want companies to save and use their personal biometric data. That’s a fair statement. I don’t want companies to hold on to my biometrics either – photos notwithstanding because that genie is out of the bottle – but when it comes to iris or fingerprints I don’t want a random company to be storing that data.
But this isn’t an issue. Most modern biometric use cases – using the biometrics on mobile devices – stores that data only on the device and nowhere else. Using your fingerprint on the iPhone to check your account balance doesn’t mean that Chase has my fingerprint. And it’s not even my fingerprint that is in question but rather a numeric template representing minutia points from ridges and valleys on my finger.
The other point of the survey was that 58% of Americans prefer passwords to biometric authentication methods. My questions to those citizens, have you tried using biometrics? It really is a lot easier to get into your mobile device with them. And you really rather type in that 12-character upper and lower chase with number and special characters rather than put a finger on a scanner or look into a camera? All right, but you’re just making life difficult.
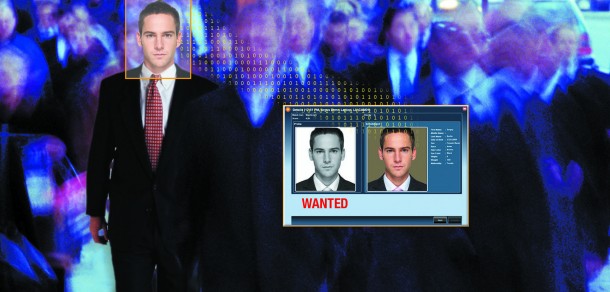
The other piece garnering headlines this month was a group of researchers from the University of North Carolina found a way to take photos from Facebook and social networking sites and use them to beat some facial recognition systems.
The system uses 3D facial models based on publicly available photos. The researchers used mobile devices to display the virtual reality-like images and beat the systems. The system gave the images motion and depth that the facial recognition systems require. The hack beat four out of five systems they tested it on.
This is a new spoof and it is interesting. Early facial recognition systems were beaten sometimes by simply holding up a photo of an individual.
This caused the vendors to add different liveness testing, individuals would have to blink or smile or do some type of facial movement before authentication could be completed. It would seem that this new approach adds some sort of animation to mimic this effect.
News of this hack has caused people to once again scream out, “biometrics aren’t secure!” But no one authenticator is completely secure. Passwords are not secure on their own, and the same can be said for any single authentication technology.
For true security there has to be layers, maybe use facial recognition but also check the IP-address, location and other data. If security continues to be a single factor hackers will always find a way to beat it. Adding layers makes it more difficult to beat, especially if the hackers don’t know which factor will be employed, maybe it’s IP address one time, maybe it asks for a PIN the next.
If enterprises continue to rely on single-factor authentication – be it biometrics or passwords – hackers will find a way to beat it if they want access.