Software-based, multi-factor alternative to hardware tokens
15 January, 2014
category: Corporate, Digital ID
Software-based authentication solutions are often considered inferior to smart cards, tokens or other hardware-based systems.
SyferLock has been trying to dispel these misconceptions with a software based authentication platform based around the PIN. Since 2007 the company has been providing it’s software based authentication technology to enterprises in a variety of markets, says Chris Cardell, CEO at SyferLock.
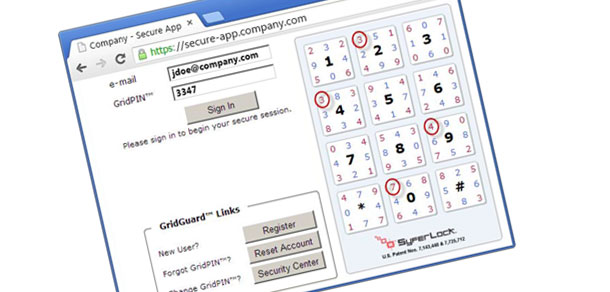
SyferLock’s technology is based on a grid and PIN system. A user registers by entering their email address or network user name. They can then watch a video on how the system works. From there they enter their password and choose a PIN and one of eight positions on the grid. For example, the PIN might be 2490 and the position could be upper left hand corner.
When the individual returns to login they enter their user name and password and then look at the grid. Instead of entering their actual PIN, 2490, they enter the numbers that are in the upper left hand corner of the boxes corresponding the digits 2, 4, 9 and 0. In the grid pictured, the result is 3347.
The red and blue numbers change with each login so the PIN entered each time is different. While the grid is used in a typical deployment, enterprises can add security by having a full QWERTY keyboard displayed. This enables upper and lowercase letters as well as digits to be used.
A smart phone application is also available. Instead of having the grid displayed on the computer screen it’s generated on the mobile device. Even if an individual loses the smart phone, a fraudster wouldn’t be able to access the system unless they had both the PIN and position, Cardell says.
SyferLock has been deployed in various markets but health care is picking up with more requirements for strong authentication because of HIPPA, Cardell says. A home health care company deployed hardware tokens and its nurses nearly staged a revolt over usability issues. The company has since switched the SyferLock and the reports back have been positive.
Other enterprises that have deployed hardware-based authentication solutions have expressed interest as well, Cardell explain. “Legacy deployments based on hardware are not always practical and we’re seeing companies move to software-based solutions,” he adds.
Software-based authentication can be cheaper because hardware doesn’t have to be purchased and distributed. Enterprises only have to purchase the software licenses. “From an administrative side it’s like keeping track of another laptop,” Cardell says. “Think about managing the tokens for an enterprise of 20,000.”
Deployment of the system can be as quick as a few hours or a few days depending on the size and complexity, Cardell says.