End of life for fed’s four levels of assurance?
Kill them? Revise them? Industry ponders options
05 January, 2015
category: Corporate, Digital ID, Financial, Government, Health
Zack Martin, Editor, Avisian Publications
The four levels of identity assurance and risk assessment date back to 2003 when the White House Office of Management and Budget (OMB) released e-authentication guidance for federal agencies.
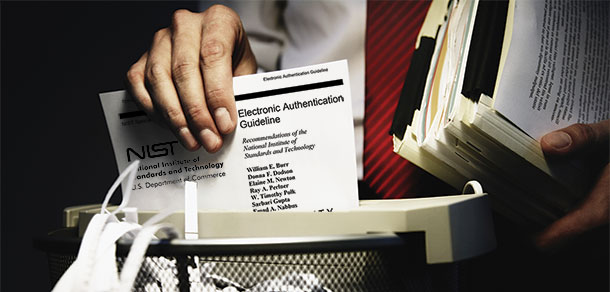
In 2006, the National Institute of Standards and Technology updated the authentication guidance in Special Publication 800-63, which received a minor update in 2013. Today, these four levels are often derided and mocked as out of touch, with one panelist at a trade show saying they should be “blown up.”
While that may be an extreme point of view, many agree that the industry has reached a point where a decision has to be made. Either revise the levels or create new ones that are more appropriate for the enterprise and consumer spaces.
“800-63 was a specific reaction to a moment in time,” says Joni Brennan, executive director at the Kantara Initiative. “The feds didn’t envision how much it would be used and they didn’t write it for the scope of who is trying to use it.”
Industry groups and NIST are taking notice that the current model for determining identity and authentication assurance needs to be revisited. NIST will be releasing a request for information before the end of the year asking the industry to comment on revising 800-63, says Paul Grassi, senior standards and technology advisor at NIST.
The hope is to come up with something that can account for and adapt to private sector led innovation and the specific risk models of relying parties. “It’s time to look at things with a different lens,” Grassi adds.
There’s a natural desire to have comparable mechanism for authentication – be it for use in a government system or an enterprise – but as time has passed the original four levels aren’t well suited for everyone. “You get the four levels, the top is mythical and the bottom is junk and the two in the middle aren’t ideal,” says Ian Glazer, a board member for the Identity Ecosystem Steering Group. “If you step away from the four levels, there could be three or there could be 300.”
Origins of the four levels
OMB took the idea of the four levels of assurance from the British – who stole it from the Canadians – who actually called it zero, one, two, three, says Peter Alterman, CEO at Safe-BioPharma and a former GSA official. “OMB felt like issuing a credential at trust levels zero wasn’t a politically wise move so they went with one instead,” he adds.
NIST took the OMB memo and put together the special publication that maps technology and technology implementations against the different levels, Alterman says. Despite the 2013 revision, he says the special pub hasn’t received a significant update since it was first issued.
The European Union is working toward an electronic ID risk assessment and mitigation framework that would use three levels: low, substantial and high, Alterman says. “The no-risk level is being taken off the table because it’s irrelevant,” he adds.
All of these ideas are going to be on the board when NIST issues its request for information on 800-63, says Grassi. The levels certainly have their issues, and while these four levels might not be the sole problem, the processes and rigidity of 800-63 may have run their course, he adds.
The hope is to get information from the private sector on how to either update 800-63 or create something new that can be used across the private sector.
“We want to know what risk models and alternative techniques have worked but aren’t aligned with our current documents,” Grassi explains. “Do we stick with four levels? Collapse to less than four since we know there is no such thing as a secure password? Do some vector or gradient based assurance standard instead that takes into account the multiple components that comprise trust in online identities?”