Identity ecosystem at core of Obama’s online plan
12 October, 2010
category: Corporate, Digital ID, Government
‘National Strategy’ proposes massive changes for electronic authentication
Create a system that individuals can use to login to a bank account, check email or keep track of research topics of interest. Give it a catchy name like “identity ecosystem” and expect it to secure all transactions while at the same time providing anonymity.
This is the task facing the National Strategy for Trusted Transactions in Cyberspace (NSTIC): Find an efficient way to protect individuals online whether they are engaged in the most secure task or the most benign.
Identifying the problem is easy. Finding and implementing solutions is an entirely different ordeal. The 36-page draft report released in June by the White House states that the strategy aims to curb the rise of online fraud, identity theft and misuse of personal information online. This involves creating an identity ecosystem that would enable security, efficiency, ease of use and confidence while increasing privacy, choice and innovation.
“The Identity Ecosystem is an online environment where individuals, organizations, services, and devices can trust each other because authoritative sources establish and authenticate their digital identities,” the report states.
The White House National Security Council led the effort on the report. The group consulted with 70 industry advisory councils and associations representing various communities, including privacy, federal government, state and local government, health care, energy, IT and the financial sectors, according to a National Security Council Press spokesperson. All told almost 4,000 comments from industry and government were collected, adjudicated and in many cases incorporated.
It is expected that President Obama will sign a directive in September or October appointing a government agency to oversee implementation of the strategy.
The directive will be similar, possibly even an amendment, to Homeland Security Presidential Directive-12 (HSPD-12), says one source. This directive, signed by President Bush in August 2004, required a standard ID credential for all federal employees that resulted in FIPS 201 and the Personal Identity Verification standards.
The strategy comes out of the Cyberspace Policy Review that recommended better authentication technology to prevent online fraud and identity theft. Some government officials, however, will say it is 10 years in the making starting all the way back when the U.S. Department of Defense issued the first Common Access Card. Subsequent credentialing efforts and this extension to the citizen are all logical outgrowth from this early program.
The report calls for an interoperable solution in which participation is voluntary. And while no specific technology is called for in the report there are references to smart cards, USB key fobs, mobile phones, software certificates and trusted computing modules. Biometric technologies are not mentioned in the report.
There were also references to some existing government identification projects, including HSPD-12 and Federal Identity, Credential, and Access Management (FICAM). Both are used as examples of how any new identity ecosystem should align with existing federal projects. Some government insiders say extending a PIV-type infrastructure to the public only makes sense.
Government officials are moving quickly to get a national strategy signed by the president and an implementation plan that includes high-level milestones. But there will be any number of steps required post-signature that will take considerable time.
“We want implementers to feel some urgency due to NSTIC’s impact on economic and national security,” says a National Security Council spokesperson. “But we want to do it right, too, and ensure that we’re not creating more problems than we solve.”
That urgency needs to be tempered with realism. The strategy calls for standard identity proofing for everyone that applies for a credential, but these standards don’t exist. The American National Standards Institute and the North American Security Products Organization have embarked on a standards creation process but this is expected to take at least 18 months. (See ID vetting sidebar)
There is also a strong possibility that legislation will have to be passed before the strategy is enabled. If private organizations are issuing the credential there will have to be issues resolved around liability and privacy. (See liability sidebar). If there is any major political opposition to the strategy, DC insiders suggest that it could hit roadblocks at this point.
And even if a strategy is published and credentials issued, where will individuals use them? Banks, hospitals and others will have to deploy back-end systems and infrastructure so the credential can be used. This won’t be cheap and it won’t happen overnight.
But the business case will be there for companies to deploy the back-end systems, says the National Security Council spokesperson.. “Better and more prolific authentication mechanisms will streamline account management and improve the automation of business processes, ultimately leading to cost savings,” the spokesperson says. “This will also minimize the collection and usage of personally identifiable information.”
Limiting the amount of personal information that providers store should make it more difficult for hackers to obtain that data. “We want to move away from the current paradigm where sensitive information is retained by every single service provider and instead move to a paradigm where individuals can chose when and what information is shared,” the spokesperson says.
“Security is always a concern and the idea is not to limit individuals to one single credential but provide individuals a choice of credentials that enable only the necessary pieces of information to be shared,” he continues. “Consumers could choose to accept the risk associated with a single credential but others will choose to carry multiple credentials.”

Putting odds on online ID
Will it be the feds, states or private sector issuing credentials?
Federal issuance
Odds: 1%
Model would be somewhat similar to passport issuance.
Pros: Because of passports something of an infrastructure is already in place.
Cons: Specter of “Big Brother” already looms large with this strategy and having the feds issue the credential would only make it bigger.
State issuance
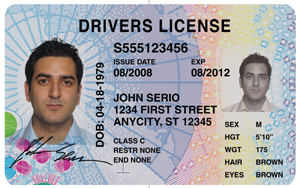
Odds: 44%
Model would be somewhat similar to obtaining a driver license with more in-depth identity vetting and issuance of a more secure document.
Pros: Individuals are already used to going to a state office to get an ID document, this process would just be a little more involved. States also have the infrastructure in place, though upgrades would have to be necessary. Since the new credentials would be voluntary states could add a revenue source by issuing the documents. Unlike private organizations, states are already absolved from liability for other ID issuance processes, so new legislation might not be necessary. And there are indications that states are becoming more interested in issuing strong credentials.
Cons: States are broke and don’t have money to upgrade infrastructure. Local government also doesn’t have much, if any, experience deploying these types of high-tech systems and credentials.
Private issuance
Odds: 50%
Some corporations are champing at the bit for this opportunity. Organizations like the Kantara Initiative are already accrediting auditors who would then certify others for credential issuance up to level three assurance–a high confidence in the asserted identity’s accuracy; used to access restricted data.
The model would likely have individuals applying for credentials in person with documentation, paying a one-time enrollment fee and then an annual fee after that to continue using the credential.
Pros: Government can pass legislation and then not have to worry much about the process. Despite all the wailing and gnashing of teeth over privacy issues on sites such as Facebook, people still use them. Private organizations, it seems, are more trusted than government in the current environment.
Cons: Private corporations don’t have much of an infrastructure in place to start credential issuance. While the economy may be starting to recover, the capital it would take corporations to get a business up and running might be too great. Liability is another issue and Congress would have to pass some type of legislation that would limit liability in case of a data breach.
It doesn’t happen at all
Odds: 5%
Government and industry officials want this strategy to proceed, but anything is possible in politics. Politicians could find a bone to pick and necessary legislation could get held up. Some mainstream media are already calling this voluntary program a national ID card and if that persists it could spell trouble.
That said, with proper education about the program people should realize it’s a necessary, if not long over due, initiative.
Summary: It’s going to be a tough race between state governments and private corporations. Cost and trust are two of the biggest issues that need to be faced and it’s going to be a matter of who can figure those two things out and make it happen.