Innovations key to securing your identity
07 January, 2008
category: Government, NFC
 Adam Shane,
Adam Shane,
Manager of Technology,
AMAG Technology
The modern history of identification technology shows us that past innovations were made in response to observable threats. This continues to be the driving factor. Shedding light on the threat dictates the path forward. However, the threat changes in unpredictable ways, and we are always in a reactive mode.
The first innovation was to the identity document itself. A very long time ago, your identity was what you claimed it to be, who knew you or could vouch for you, and possibly any public record about you. The threat was the stranger–the person who just showed up and no one knew anything about him. Eventually, identity papers such as birth certificates became available. A desire to emigrate created the need for passports and driver licenses.
Fast forward to more modern times where you likely have multiple documents in your possession that define your identity or are related to your identity. Today the threat is not the fact you don’t know the stranger who rode into town, but that someone might adopt your identity, borrow money or purchase items on credit in your name. Some refer to this threat of identity theft as a lack of privacy, but it is not privacy that we seek today as much as a secure identity.
To combat this threat our identity documents have to change to meet the demand for secure identity. There are many challenges to safely securing one’s identity. For instance, a Social Security number is issued by the United States Government to its citizens. There is no security on this information, and the prevalent use of this number makes it easy to obtain. Also, there are few (if any) minimum requirements on individual states in how they vet one’s identity when issuing driver licenses. In addition, those documents are easily forged as are birth certificates and other identity papers.
However, there have been a number of recent innovations in this area. The new ePassport includes a secure contactless device (smart card) that performs encryption on the chip prior to releasing identification information over the contactless interface. The Real ID Act, signed into law in 2005 but not scheduled to take effect until 2009, requires minimum state standards for driver licenses and other identity credentials if they’re to be accepted by Federal agencies. Since airlines are also included, all states are expected to comply.
Will these advancements prevent identity theft? Most professionals in this field agree that this is not the complete solution. There are many more areas that need to be covered, but it is certainly a step in the right direction.
Another issue that needs to be addressed is the misuse of the Social Security number. It should be kept confidential and not used for many of the mundane purposes it is today. Financial institutions want to classify their risk in loaning you money so they want to associate this loan request to the rest of your credit history. Insurance companies want to make sure that you are not taking advantage of them and want to match you against your insurance coverage. The challenge then, is to assert your identity to meet those business demands, but to protect yourself from someone else using that identifier.
There are technologies available today that will aid in our fight to secure our identities. Smart cards are becoming more prevalent, particularly among credit card issuers. While parts of the world outside the U.S. have been using this technology longer than we have, it is the large U.S. market that these companies cherish. But we are a fickle bunch, and we are slow to adopt new technology. Yet, smart cards are capable of using data encryption and Public Key Infrastructure (PKI) that hold the promise of securing individual transactions as well as providing proof of identity.
We can expect more secure ID innovations over the next five years and our ability to adopt the technology in an intelligent and insightful manner will be the key to our ability to manage the threats.
The evolution of the identity credential
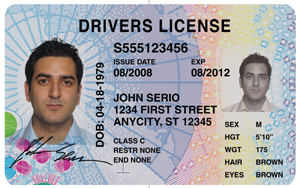
The credential we carry to establish our identity has changed over time mainly due to the available technology of the era, but it is hampered by extraneous pressures. Consider today’s driver license: the card has our picture and an ID number with other biographical information. There is a magnetic stripe, but the only anti-counterfeit technology is in the holographic image or laminate that is applied.
The same is true for corporate identification badges. However, these corporate badges are also often used for access control, and that has driven companies to incorporate newer technologies to prevent counterfeiting in an effort to shield corporate assets. These badges have gone from a flash pass (a security guard or peer simply checking that the image on the badge resembles the person holding it) to a magnetic stripe to a contactless ID card.
Today one of the most advanced identity credentials is the US Government Personal Identity Verification (PIV) card. This credential uses smart card technology in both a secure contactless as well as a contact interface mode. The present card is basically the first generation of this application. The next generation will utilize digital certificates and PKI to provide a truly secure transmission of identity information. Furthermore, the use of PKI makes counterfeiting of the credential nearly impossible.
About the AVISIAN Publishing Expert Panel
At the close of each year, AVISIAN Publishing’s editorial team selects a group of key leaders from various sectors of the ID technology market to serve as Expert Panelists. Each individual is asked to share their unique insight into what lies ahead. During the month of December, these panelist’s predictions are published daily at the appropriate title within the AVISIAN suite of ID technology publications: SecureIDNews.com, ContactlessNews.com, CR80News.com, RFIDNews.org, FIPS201.com, NFCNews.com, ThirdFactor.com, and DigitalIDNews.com.