Liveness detection forces hand of biometric spoofers
Still 3D printing, advancing techniques help fraudsters up the ante
21 April, 2014
category: Biometrics, Digital ID, Library
For as long as biometric technology has been used for access to secure areas there have also been attempts to fool these scanners. Combating biometric spoofers is an ongoing process, and with biometric technology positioned to serve a key role in mobile security’s future, it is getting even more attention.
The real strides in spoof mitigation have been taking place in the arena of liveness detection. “Primarily we’re working in fingerprint liveness detection on the software and algorithm side,” says Stephanie Schuckers, Associate Professor at Clarkson University.
The term “spoofing” is something akin to a Wiki entry, as the definition continues to grow and change over time. So much so that if you were to ask five different people to define spoofing, you may well get five different answers.
To combat this confusion and better characterize the threat, Schuckers and others in the field are coining a new term – presentation attack. “Spoofing is a general term that can refer to a lot of different things. Is spoofing trying to be a specific individual? Is it just using a fake biometric? There’s still a lot of confusion,” says Schuckers. “We’re cementing our vocabulary so we can all speak about the same thing.”
The term ‘presentation attack’ is fairly specific, referring to how one presents a biometric and tries to interfere with the operations of the biometric system.
When it comes to presentation attacks, key elements to consider are whether the image applied to the sensor is a real body part and whether the collected image actually belongs to the person who provides it. Enter liveness detection.
The methodology
In what is likely the most high profile spoofing attack in recent history, Apple’s Touch ID fingerprint sensor fell victim to attack two days after its release. What, then, does the spoofing process entail?
According to Mark Cornett, COO of NexID, to spoof a fingerprint recognition system the first step involves the acquisition of the original biometric in the form of a latent, or lifted, print. This can be obtained from an appropriate surface such as a glass, doorknob or touch screen device – a process that according to Cornett is as simple as it is quick.
“Acquiring latent prints can be done with a variety of methods all of which involve highlighting or enhancing the print, and capturing it via lift tape or photography,” explains Cornett. “The captured print is then digitized, a step that can be done very quickly.”
From the digitized print, some attacks are attempted using a high-resolution image of the fingerprint, which is then presented to the scanner. This method may seem simple, but it gets more sophisticated.
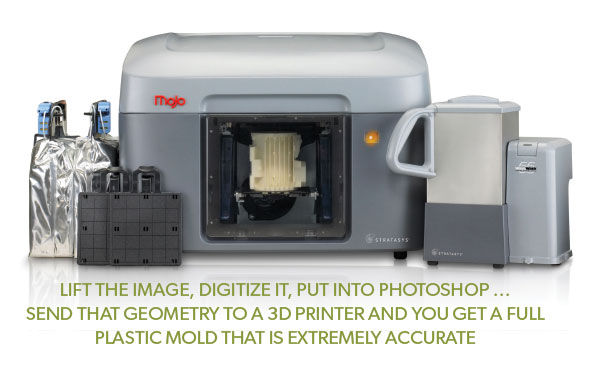
A more complex method requires the spoofer to create a mold from the fingerprint image, which is used to cast a dummy finger using a chosen spoof material. Several techniques for creating the mold exist. “When printing the image onto transparency film, the thickness of the printed ink is actually enough to cast a 3D spoof,” he says. “Etching the image on a blank printed circuit board or converting the 2D image to a 3D file and printing this out using a 3D printer also work. Adobe Photoshop can easily facilitate this 2D-to-3D conversion.”
Cornett and the NexID team focus on the non-cooperative side of presentation attacks, lifting latent prints and using them to make molds.
“We work with acetate molds, etched molds and we’re now looking into 3D printed molds,” reveals Cornett. “3D printed molds are particularly interesting because you can lift the image, digitize it, put into Photoshop – and make the ridge-valley differential as shallow or deep as you want. Send that geometry to a 3D printer and you get a full plastic mold that is extremely accurate.”
Productizing the spoof
The increased adoption of biometric recognition systems has given rise to a new industry, the business of liveness detection. As a result, Clarkson University spinoff, NexID, was formed to commercialize early research in liveness detection. Not long after, the company began drawing interest from fingerprint manufacturers.
The company developed a software-based liveness detection application. “It’s an extractor-based application that mimics matching software, only its features pertain to the inherent differences between live and spoof-generated images,” explains Cornett. “It conducts image processing and statistical analyses based on a set of algorithms and roughly 160 features.”
NexID consults with sensor manufacturers to identify chinks in their products’ armor, along the way finding out which spoof materials are most effective and prescribing patches for vulnerabilities. These patches can take the form of tweaks to the NexID software algorithm, which tunes it to best serve the specific sensor. In the field, the software application then provides a score back to the target device, at which point the user application can either accept or reject the liveness of the finger image applied to the reader.
While NexID’s offerings are strictly software based, there are other spoof mitigation measures available. “Scanner and sensor manufacturers are beginning to take steps to incorporate spoof mitigation and liveness detection techniques into their devices,” says Cornett. “Some involve collecting additional biometrics from which they can infer liveness, such as temperature or blood flow.”
“Others are measuring deformation of the material being scanned – as compared with skin deformation – and still others are using software and image processing to discern differences between live and spoof,” he explains.
On the horizon international standards are being developed to establish common presentation attack detection tests for scanners and sensors.