Lock down your networks with active segmentation
30 September, 2015
category: Corporate, Digital ID, Financial, Government
TK Keanini, CTO, Lancope
Over the last few years, the cyber security industry has undergone a paradigm shift from focusing solely on attack prevention to also taking measures to identify and mitigate threats that have already managed to infiltrate perimeter defenses. Threat actors are not breaking in anymore, they are simply logging in.
For many organizations, this is new territory. Instead of simply implementing firewalls and anti-virus and checking off the “security” box on the to-do list, companies are taking a hard look at their network and scrambling to lock down everything in the face of sophisticated attackers. For some this means hiring a Chief Information Security Officer, and for others, it means employing a security consultant, but everyone should be considering access control and segmentation.
While the fear, uncertainty and doubt surrounding cyber security tends to be counterproductive, organizations should still be making prudent security decisions based on the fact that at some point their network will likely be compromised. Attacks involving stolen access credentials are on the rise, and in many cases, security personnel have no way of identifying who is a legitimate insider and whose login information has been stolen by cyber criminals.
Fortunately, gaining access to a network and actually stealing valuable data are two completely different things, and there are a few measures that security professionals can take to limit the likelihood of success and the scope of a data breach. Properly segmenting the network and ensuring the efficacy of access control policies is a primary factor in keeping security events from becoming high-profile breaches. Each transition point from one boundary to another is an opportunity for observation, analysis and mitigation.
Keep your hands to yourself
In an unsegmented network, everyone can touch everything. Marketers can access engineering documents, engineers can access financial documents, and there are little to no internal barriers around even the most sensitive information.
In some cases, even third-party contractors have access to internal systems and data stores. For instance, the 2013 data breach at Target was linked to credentials stolen from a third-party HVAC vendor.
The problem with this scenario is it hands over all network assets to any intruder who manages to make it past perimeter security. One hacker can successfully exploit one attack vector and steal financial data, intellectual property and personal information on employees and customers all at the same time. Even more frustrating is that there is no reason why every organizational insider needs access to every system and document. It is a needless risk.
Here’s another analogy. If you had to store a pile of gold in your home, would you lock it in a safe, or would you leave it on the kitchen counter? More than likely, you would put as many locked doors between that treasure and the outside world as possible. So then why would you allow your data, which can be worth much more money than gold, to sit where anyone can access it?
Active segmentation is your locked door
By dividing network assets into separate zones based on the needs of different insider roles, the risk can be spread among all of the access credentials. Instead of having a single point of failure guarding the data, only small pockets of data can be accessed with individual logins. If done correctly, network segmentation significantly increases the organization’s security posture without disrupting business functions. Additionally, the longer an attacker spends trying to access data within the network, the longer the security operations team has to identify them and remediate the situation.
The devil is in the details, however. Segmentation has been around for years, and most organizations shy away from it because it is traditionally difficult to implement and maintain. Extensive access control lists must be created, and any change has to be implemented across many different points of enforcement. This can quickly become a headache in large corporate networks with thousands of users and different network environments, such as a cloud deployment.
Software-defined segmentation is one important step to overcoming this problem. With software-defined segmentation, organizations can abstract policies away from IP addresses and instead leverage user or machine identities to implement and maintain a centralized policy management system. This can cut down on the tedium of maintaining an agile segmentation strategy while also remaining effective in high mobility or complex network environments.
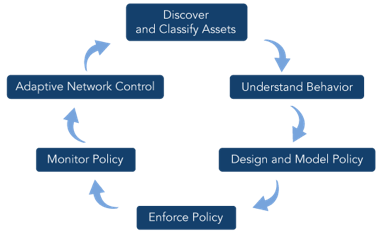
To take full advantage of software-defined segmentation, administrators can utilize active segmentation, an intelligent methodology for implementing and maintaining effective access control with minimal disruption to business. Like all great approaches to cyber security, active segmentation is a cyclical process that involves continuous observation, assessment and adaptation to changing circumstances and environments.
When used correctly, active segmentation consists of:
- Identifying and classifying all network assets based on role or function
- Understanding user behavior and interactions on the network
- Logically designing access policies
- Enforcing those policies
- Continuously evaluating policy effectiveness
- Adjusting policies where necessary
Network visibility enables effective segmentation
In addition to software-defined segmentation, nearly every component of active segmentation requires comprehensive network visibility. Understanding who is on your network, what they are doing, who accesses what assets and what normal day-to-day network activity looks like is critical to properly segmenting the network. Without visibility, you have no way of knowing how to design proper policies, which could potentially deny access to critical assets by legitimate users, or whether the policies are implemented correctly, which could leave the network vulnerable.
With the right kind of network visibility and monitoring tools, administrators can model the segmentation policies to alert on any activity that violates intended access control. This adds a continuous layer of verification. Since networks are constantly changing and growing, mistakes can be made. Maybe a forbidden port was left open or last minute changes left insecure access points to a protected network. By employing a solution that continuously monitors traffic for policy violations, misconfigured machines can be quickly identified and remediated.
This constant cycle of planning, assessing and adapting allows the organization to gain all the benefits of segmentation without the headaches of traditional methods. Furthermore, by constantly evaluating the environment and policy efficacy, active segmentation retains its effectiveness regardless of network growth and change.
Lock Away the Crown Jewels
The cyber threat landscape is too varied and extensive to afford a single gate between your data and a potential hacker. It is simply too likely that you will breached, and when it happens, all of your data could be stolen in a single instance. By harnessing the power of network visibility and active segmentation, any would-be attacker is stuck with a limited amount of data. Instead of stealing your organization’s crown jewels, they will have to settle for something from the souvenir shop.
Lancope Inc. is a provider of network visibility and security intelligence to protect enterprises against today’s top threats.