Merging FIDO and PIV could help Feds achieve strong authentication goals
Lightweight mobile keys to extend derived credentials across on-premise and SaaS apps
17 March, 2017
category: Digital ID, Government
The FIDO Alliance wants the U.S. government to leapfrog the obstacles to pervasive PKI authentication using FIDO and PIV. Agencies have deployed the PIV credentials extensively but still struggle to extend the cards’ use for digital identity in a widespread manner. Certain applications are PKI-enabled, but the majority of use cases remain the realm of one-off authentication mechanisms or simple user name and password.
In a new white paper, Leveraging FIDO Standards to Extend the PKI Security Model in United States Government Agencies, FIDO spells out how its lightweight approach to asymmetric cryptography could help the government meet the goals of HSPD-12 and the virtual mandate imposed by our current data breach culture.
FIDO reminds readers that when HSPD-12 was issued in 2004 it called for, “flexibility in selecting the appropriate level of security for each application.” The Presidential Directive did not mandate creation or use of a single credential nor did it prohibit various approaches to meet its goal of physical and digital access in the Federal enterprise. The idea that all access should be secured by a PIV card came about when FIPS 201 was released in 2005.
There was good reason back then to limit HSPD-12 to a single technology, largely because realistically available options to achieve PIV-level security did not exist at that time. But the report appropriately points out that, “twelve years have passed, and authentication technology has evolved and improved significantly – creating an opportunity for agencies to leverage the flexibility that was originally called for in the 2005 directive.”
Complementing Fed authentication via FIDO and PIV
The group’s proposal is expand the current use of PIV’s derived credentials to include a lightweight key pair based on the FIDO standard — effectively merging FIDO and PIV.
Currently, a public and private key can be spawned from the card’s cryptographic profile for use on mobile devices. This fixes one part of the PIV card challenge as the new derived credentials can be presented across networks without the need for a card reader. But it still is full blown PKI so any application or service that consumes the derived credentials must be PKI enabled. This has been the second part of the PIV challenge as PKI enabling applications – both legacy and new – is not an easy process.
If a lightweight FIDO asymmetric key pair was also derived from the original PIV credential and housed on the mobile device, it would be usable for authentication within a much wider set of applications. For legacy services that cannot support PKI, the FIDO keys would still be viable. And for the world of web services and SaaS applications, these new government credentials would be accepted virtually out of the shoot.
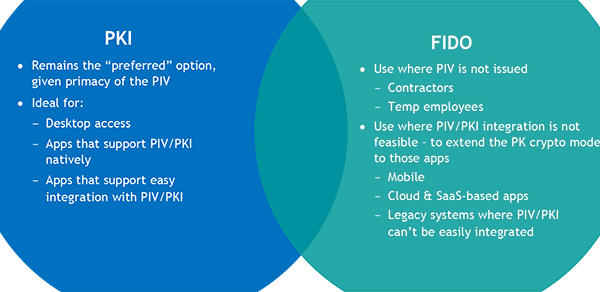
Obviously, an agency would be encouraged to choose strongest available authentication mechanism available for a specific access transaction. If full-blown PIV card presentment were doable, that would be the preferred route. But in cases where this is not possible, PIV derived credentials would be next followed by FIDO derived credentials.
The key to remember is that this vast majority of authentications are now unsecure relying on shared secrets, passwords and one-off authentication techniques. Even if the lightweight derived credentials are not quite as strong as the initial smart card presentment envisioned in FIPS 201, they are far better than the current approach.
Additionally, this approach could extend the use of strong government issued credential to a larger population of Federal employees and contractors. PIV and PIV-I cards are not issued to all individuals accessing agency networks and services so this could prove a cost effective, rapid approach to authenticating these individuals.