Put identity at the center with a federated service
New demands, serve legacy applications and evolve your aging directory infrastructure
18 December, 2014
category: Corporate, Digital ID
Lisa Grady, Senior Solutions Architect, Radiant Logic
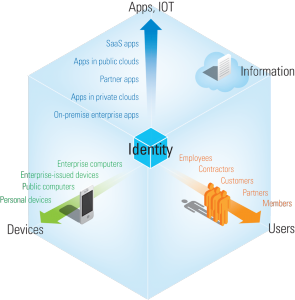
The world of access and security is exploding. Today’s identity systems are tasked with empowering new categories of users and agents — everything from third-parties, partners and customers to machines and automated processes — while reaching into the cloud to enable new applications and enabling access from a world of new devices. We’re moving to increasingly federated systems to manage these new realities, but our identity infrastructure hasn’t kept pace — and many of our mainstays Lightweight Directory Access Protocols are nearly at the end of life.
Today’s legacy infrastructure can’t keep up with new demands — and the problem will only get worse as we move from Identity and Access Management to Identity and Relationship Management, shifting the focus from the relatively simple issue of access to the multi-layered demands of relationship management and contextual communications. And it will become unimaginably complex when all our devices—from home thermometers to smartphones, from medical devices to refrigerators—need to be treated as constituents within the system.
The acceleration of digitization of all aspects of our life means that the quantification of every aspect of an individual and its identity is growing by the day. But all these digital attributes that simplify our lives can do their magic only if they are attached to a digital identity — and what that identity means will keep shifting and growing as technology evolves. From the social graph to security contexts, the multiple aspects of our digital identity need to be managed, so that our proxy lives — our “avatars” in the digital world — don’t get caught up in the chaos of privacy concerns, security breaches, and ultimately, losses of identity.
So how do we prevent this “digital identity complex,” both as individual stakeholders and interested organizations? And how do we retrofit our infrastructures to respond to these new challenges and opportunities?
Putting federated identity at the center
First, we put identity where it belongs—right at the center. After all, this new flow of information is always based around people, no matter what role they play. Think of how Steve Jobs changed the old world of PCs, phones, and watches into an “I”-driven world of Apple, with the iMac, the iPhone, and the iWatch. And consider the coming world of the “Internet of Things,” where all these millions of devices, each with its own identifier, must still be linked to the person who owns them.
Our identity systems must grow, in both capacity and flexibility, to meet this exploding demand. We must examine the forces driving change within IAM and look at how the current storage and identity representation based on the directory structure could expand and change to meet current and future demand. We’ll look at harnessing the flexibility of data virtualization and federated databases and combining that with the power of big data and cluster computing to create a new directory — an identity service for for the new digital age.
The new truths of identity:
- Manage Globally, Act Locally: Your identity will always come in a variety of forms, so you need a way to integrate without centralizing, federating that identity without imposing a rigid structure, such as the over centralization of the enterprise directory or the inflexibility of the metadirectory. Such a process respects the contribution of each silo without getting stuck in the limitations of a siloed world, delivering one uber-central system.
- Build a Federated Identity Service Based on a Common Data Model: Use virtualization to unify and rationalize identity information from across diverse sources, so you’re working from a common platform with all the attributes that describe each person. This new global model marries the performance of LDAP and the data management capabilities of SQL, while giving each application the exact view of identity it requires and leaving each backend store authoritative for its own data.
- Give New Life to the Old Directory: Because identity is managed mainly in directories, we need a way to reinvigorate our aging systems, revamping directories using cluster-based computing principles and big data technologies. As we move to more context-driven computing, we also need to recognize the importance of hierarchies and search technology. Redefining databases and directories into systems based on search technology and keywords will also help open the door to more context-aware services.
Businesses should learn how to migrate to a more modern directory system without disruption today, while laying the groundwork for a more context-aware future.