Technology choices abound for stronger digital identity
Password replacement methods take many forms
22 September, 2014
category: Corporate, Digital ID, Financial, Library, Smart Cards
Each month that passes seems to bring about another password breach or Internet vulnerability. Enterprises are aware of the insecurity of passwords and actively seeking out different digital identity and authentication technologies.
Multi-factor authentication can go a long way to preventing many of these breaches as passwords are still the number one way hackers are gaining access to information on computer networks, according to the 2014 Data Breach Investigation Report from Verizon.
Two out of three breaches exploit weak or stolen passwords, making a case for strong two-factor authentication, says Jay Jacobs, co-author of the report and a principal at Verizon Business. “Across the board, hackers are focused on compromising identities,” he explains.
The 2014 data breach report analyzes more than 1,300 confirmed data breaches along with more than 63,000 reported security incidents. In an attempt to gain a better understanding of the cybersecurity landscape, for the first time the report includes security incidents that didn’t result in breaches.
Over the entire 10-year range of this study, the tally of data breaches exceeds 3,800.
Weak or default passwords led to many of the point-of-sale attacks last year. Most of these devices are open on the Internet and small merchants either don’t password protect them, use weak passwords or leave the default ones in place.
“The big problem was that the same password was used for all organizations managed by the vendor. Once it was stolen, it essentially became a default password and the attackers also gained knowledge of the customer base. Armed with this information, the familiar modus operandi of installing malicious code that captured and transmitted the desired data began,” the report states.
Verizon recommends that merchants make sure all passwords used for remote access to point-of-sales systems are not factory defaults, the name of the vendor, dictionary words, or otherwise weak choices. If a third party handles this responsibility they need to make sure they are adhering to this requirement. Also, two-factor authentication is crucial.
Another area where credentials were targeted was with web app attacks. These attacks happen in one of two ways: exploiting a weakness in the application or using stolen credentials to impersonate a valid user.
Within the financial industry, for example, hackers focus on gaining access to the user interface of the web-banking application.
“They target user credentials and simply use the web applications protected with a single factor – a password – as the conduit to their goal. The tactics used by attackers are all the usual suspects: a) phishing techniques to either trick the user into supplying credentials or installing malware onto the client system, b) the old stand-by of brute force password guessing, and c) rarer cases of targeting the application through SQL,” the report states.
Verizon again knocks the single-factor password for these attacks and recommends that that enterprises mandate alternate authentication mechanisms.
Many different approaches address password weakness
To combat these threats and bolster online security, vendors are coming up with a wide range of authentication approaches and technologies. The commonality is to make online identity more secure without adding burdensome hoops.
The term “friction” is often used in conjunction with online identity. This doesn’t refer to the act of physically rubbing a token on to laptop or smart phone, but rather how much more difficult an authentication technology makes it to gain access to a web site or service.
Simply put, no authentication scheme is without some friction. But the aim of technology providers and the replying parties who will deploy these new systems is to develop a scheme that is as friction-less as possible. Here are a few of the many companies working on solutions.
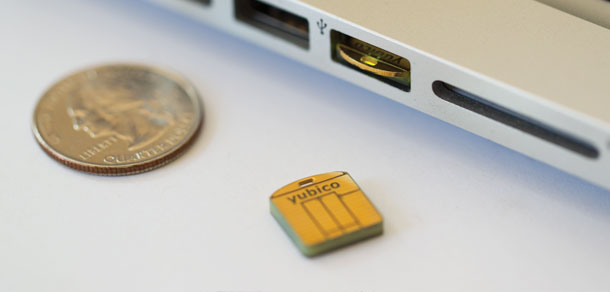
Yubico
Yubico offers a driver-less USB key called a Yubikey that serves as a second factor of authentication, says Stina Ehrensvard, CEO and founder of the company. Google uses the technology internally and seven of the top 10 Internet firms also use it for logical security within the enterprise.
To securely authenticate software engineers to production networks and servers, Facebook deployed the Yubikey solution for quick and easy authentication of employees.
The Yubikey is one of a series of two factor authentication options Facebook employees can choose. Using the cloud-based platform from Duo Security, an array of options – push, SMS, mobile, voice – can be supported.
With Duo, users are given a choice of device and method each time they authenticate. Additionally, Duo supports all phone types, from smart phones to landlines, and lets users authenticate with a variety of authentication factors including the YubiKey.
The YubiKey Nano is designed to stay inside the USB-slot once inserted. To authenticate, users simply press the device and a passcode is instantly and automatically entered, there is no need to physically re-type passcodes.
Web developers can use widely available open source tools to create systems that enable the YubiKey for access, Ehrensvard says. She compares the Yubikey to a smart card in a keyfob form rather than a basic OTP device.
“One-time passcode technology is good but there are emerging threats such as man-in-the-middle or man-in-the-browser attacks. It is better than passwords but not as good as smart cards,” she says.
Smart card technology has its drawbacks as well, Ehrensvard explains. “Smart cards are complex, need readers, middleware and a Certificate Authority,” she says. “We’re trying to take smart card technology to the mass consumer market by removing the barriers and complexity.”
The Yubikey doesn’t require any middleware, drivers or a Certificate Authority. Instead the authentication is placed in the browser, enabling Web developers to build authentication protocols that take advantage of the device.
In its default mode, the YubiKey works by emitting a one-time passcode by emulating a USB keyboard. As almost all modern computers support USB keyboards, the YubiKey requires no additional client software.
A user inputs a password, inserts the YubiKey into the USB port and then presses the button to emit the OTP. The OTP is verified by the software or service supporting the Yubikey, enabling secure login in under a second.
Each time a new OTP is generated, it invalidates all previously generated passcodes. This means that even if a YubiKey is recorded, it cannot be used again to access a protected site or service. Each OTP is unique to the YubiKey it’s generated from, and cannot be duplicated or copied to another device.
Yubico is a member of the FIDO Alliance, an organization dedicated to bringing high-assurance authentication to the masses. The alliance is working on a Universal Authentication Framework and a Universal Second Factor.