The continuously-connected information future
18 January, 2011
category: Corporate, Digital ID
How will we be identified in the future?

The world of information is currently undergoing convulsions on a tectonic scale. There is a growing expectation that everyone will soon be able to access all their information resources, including communications, with anyone they wish–from anywhere and at any time. The coming changes will have significant implications for the ways in which we both work and play.
But, on the way to this continuously-connected information future the technological and societal forces are not yet fully aligned. Progress along the path awaits answers to some difficult security questions, including: how can the user conveniently assert his or her identity and privileges across all communication channels, with an appropriate level of assurance while respecting their reasonable expectations for privacy?
At the heart of the issue is the question of identity credentials; what do they look like and how do they work? Credentials come in many form-factors. And, today, the needs of various information platforms result in having too many credentials–passwords, passports, licenses, access badges, payment cards, loyalty cards and keys to the house, car and office.
While there are dangers in having a single credential that we use across all platforms, we currently have to deal with too many and some can be very frustrating.
Solutions are available to improve convenience but too often convenience must be bought at the price of privacy and assurance. And, privacy and assurance raise issues of liability that can only be overcome with a suitable business model.
One popular solution is to host credentials “in the cloud.” This approach helps ensure that the associated identity attributes are accurate, up to date, consistent and available.
While cloud-based solutions are capable of closing the convenience gap, there are currently no cloud-based business models that can satisfy the privacy and assurance needs. Credential form-factors that come up short on any one of those fronts are not going to gain user acceptance.
The alternative to cloud-based solutions is a wallet-style credential, including smart cards, USB tokens, smart phones and electronic identity documents. These form-factors can more readily satisfy the privacy and assurance requirements of a broad range of information platforms.
But it is not possible to use a single wallet-style credential across a broad range of platforms. There just isn’t a common way–at least not yet–of interfacing the credential to all the necessary platform types.
One limitation of wallet-style credentials is that they can make it difficult to recover from a loss or damage. In this situation the user is faced with repeating the enrollment process from scratch, which is likely to cause frustration. Other approaches exist, such as an emergency cloud-based back-up or duplicate credential.
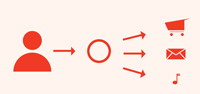
In order to fully open the door to the continuously-connected information future, a credential must be accepted on the Web, on the move, over the phone and in person. It must unlock devices, networks, applications and doors.
And, maybe most surprisingly, it must be fun to use. While that may be asking too much, it certainly must not be frustrating to use. Otherwise, users will continue to look for ways to avoid using it properly.
In order for a single credential to work with a broad range of information platforms, some order has to emerge in the range of interfaces–whether wired or wireless–that are used for accessing credentials. This is critical so that one credential form-factor can interact “out of the box” with every type of computer, mobile phone, POS terminal, inspection terminal and turnstile.
There can be no single answer to the question of an acceptable credential type for the continuously-connected information future. In addition to the platform interface differences, cultural and generational diversity make support for different credential types essential.
The smart phone form-factor is attractive from several points of view; it has a keyboard, a display and an internal source of power. And its hardware cost is “sunk” by its primary use. But smart phones are still cost-prohibitive for many users and any multipurpose platform, like a smart phone, has the potential to be less secure than its dedicated counterpart.
The smart card form-factor is also attractive–because as long as its carried in the user’s wallet–it does not represent an additional item that the user is required to have on his or her person.
It does lack a direct user-interface and usually has no internal source of power. But these limitations can be overcome. In addition, the hardware cost has to be borne entirely by its use as an identity credential.
The future of identity credentials is becoming clear. While obstacles remain, it is possible to see how those obstacles may be overcome in the next few years. Governments can play a key role in bringing about the continuously-connected information future.
And while governments may be reluctant to get involved in what might otherwise be viewed as a commercial issue, they are in the best position to overcome the assurance, privacy and liability issues–thereby eliminating the obstacles to the emergence of suitable business models. Their involvement is essential in order to ensure the online safety of their citizens and to further stimulate the online economy.
About the AVISIAN Publishing Expert Panel
At the close of each year, AVISIAN Publishing’s editorial team selects a group of key leaders from various sectors of the ID technology market to serve as Expert Panelists. Each individual is asked to share their unique insight into what lies ahead. During the month of December, these panelist’s predictions are published daily at the appropriate title within the AVISIAN suite of ID technology publications: SecureIDNews, ContactlessNews, CR80News, NFCNews, DigitalIDNews, ThirdFactor, RFIDNews, EnterpriseIDNews, FinancialIDNews, GovernmentIDNews, HealthIDNews, FIPS201.com, IDNoticias es.