‘Cyber Sprint’ dramatically increases PIV usage
04 August, 2015
category: Digital ID, Government, Smart Cards
In the wake of the U.S. Office of Personnel Management data breach, federal agencies undertook a “cyber sprint” last month to better secure federal networks and systems and increase PIV usage.
A priority of the sprint was adding two-factor authentication for user access. The cause of one of the OPM breaches was a corrupted contractor credential which lead to hackers accessing the federal systems and more than 4 million records.
Agencies made significant steps toward increasing PIV usage during the sprint, according to the White House.
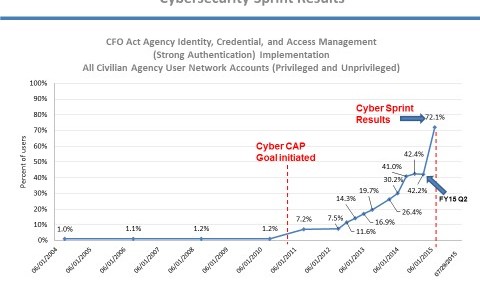
Federal agencies increased their use of strong authentication for privileged and unprivileged users from 42% to 72% – an increase of 30% since agencies last reported their quarterly data on Performance.gov.
Among privileged users usage of PIV has increased significantly. Federal agencies increased their use of strong authentication for privileged users from 33% to nearly 75% – an increase of more than 40%.
Hackers target privileged users in an enterprise because they possess elevated access to federal systems and enable other employees’ access to different systems. They are the ones that enable employee’s access to new applications, systems and networks.
At the time of the OPM breach, eighteen agencies did not mandate that privileged users login using PIV authentication. That has since changed. Thirteen agencies, or more than half of the largest agencies – including the Departments of Transportation, Veterans Affairs, and the Interior – have implemented the same level of strong authentication for nearly 95% of their privileged users.