Cybersecurity: Taller walls, deeper moats but the front gate is unguarded
27 July, 2015
category: Corporate, Digital ID, Financial, Government, Smart Cards
Imagine walking into a warehouse store that, instead of selling bulk amounts of toilet paper and paper towels, sells addresses and house keys. Now imagine that these address and keys open doors that already belong to other people.
This warehouse actually exists, albeit virtually, and fraudsters visit to buy email addresses, account logins and passwords for more than a billion accounts. For a bit more, they can add Social Security numbers, physical addresses and other demographic information. All of this is made possible thanks to the dark web.
Database and password hacks are so commonplace, that unless a breach registers in the millions it won’t even garner attention in the press. In recent months, these breaches have left everyone from casual web surfers to the president of the United States calling for efforts to better secure cyberspace.
The majority of these efforts seem to revolve around building taller towers and deeper moats to prevent hackers from gaining access. What’s lacking, however, are the efforts to add strong authentication and advanced identity and access management to make sure only those authorized are enabled to gain access. The best firewalls and intrusion detection won’t matter if someone has keys to the front door. Making identity a foundational component to cyber security, then, is paramount to any attempt to solve the issues facing enterprises.
The number one way hackers are gaining access to information on computer networks continues to be the misuse of usernames and passwords. So says the 2014 Data Breach Investigation Report from Verizon, citing that two of every three breaches exploit weak or stolen passwords.
The U.S. government is also feeling the pain. More than half of cyber intrusions to federal agencies could have been prevented using strong authentication, according to a report from the White House Office of Management and Budget. The annual report to Congress on the Federal Information Security Management Act (FISMA) details how agencies are still behind when it comes to using PIV credentials and strong authentication technologies.
Password problems plague federal agencies
The U.S. government is not immune to cyber threats. While many agencies have taken steps to improve identity and access management, a lot of work remains to be done as a recent report shows more than half of cyber attacks could have been prevented with strong authentication.
Federal agencies issue employees PIV smart cards for use for physical and logical access. However a report from the White House Office of Management and Budget shows that in too many cases, the credentials have not been enabled for widespread logical access.
The Department of Veteran’s Affairs has more than 350,000 users accessing information with only usernames and passwords, while the State Department has 100,000. On the positive side, the Department of Homeland Security leads the way for PIV access with almost 250,000 employees using the credentials followed by Health and Human Services with almost 100,000. The Defense Department was not included in this survey but requires its employees to use the Common Access Card for strong authentication.
While the substantial number of unprivileged user accounts – of which there are more than 5.3 million – are able to access Federal networks with only a username and password, the more troubling concern is the number of privileged accounts that require only username and password.
Unprivileged user accounts are the ones regular employees use to access email, applications and services. Privileged accounts are the administrators of those systems and are typically the ones that are able to create new accounts and access additional information. Privileged user accounts, of which there are 134,287 across the government, possess elevated levels of access to, or control of, Federal systems and information, increasing the risk to resources if their credentials are compromised.
There are 18 agencies that do not require a majority of their privileged network users to login using two-factor PIV authentication. Health and Human Services and the State Department are the worst offenders when it comes to having privileged users accessing networks with usernames and passwords.
Additionally, US-CERT found that 52% of 2014 cyber incidents were related to or could have been prevented by strong authentication implementations. Strong authentication for civilian agency user accounts is at only 41%, well below the 75% target.
E-Gov Cyber reviewed agency performance against authentication-related FISMA Metrics. As part of the reporting process, agencies describe the different authentication methods employees use to gain access to Federal information and networks.
Of the 24 agencies evaluated, 16 had weak authentication profiles, enabling the majority of unprivileged users to login with user IDs and passwords alone.
This makes unauthorized network access more likely as passwords are much easier to steal through either malicious software or social engineering.
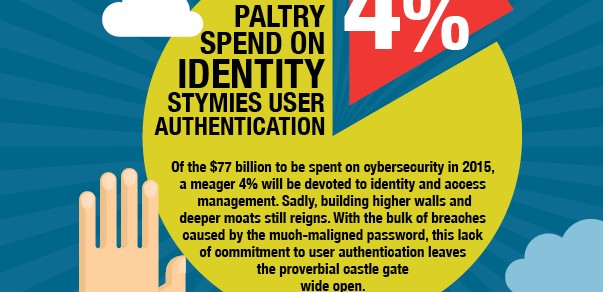
Budgets also don’t seem to be going to identity and access management. In 2015, Gartner Research predicts that $77 billion will be spend on IT security, but just 4% – or $3.3 billion – be spent on identity and access management related products and services. Enterprises are investing in firewalls, secure gateways and other security systems – but still neglecting the proverbial front door key.
“There’s no silver bullet for cybersecurity,” says Jeremy Grant, managing director at the Chertoff Group and former director of the National Program Office for the National Strategy for Trusted Identities in Cyberspace. “But if you’re getting hacked because of your password technology that’s a pretty good sign you should do something with identity.”
Information security professionals have never put a focus on identity, says Jeff Nigriny, president at CertiPath. “The bulk of product development has been centered on anti-intrusion detection for the network,” he explains. “Identity has revolved around creating a better password.”
People relegate the identity issue to the backburner because they don’t want to do something that’s difficult. It’s a battle getting people to take the identity threat seriously and put some simple things in place.
Despite the Verizon and FISMA reports, enterprises aren’t taking identity issues seriously, Grant says. “Identity is the red-headed stepchild of cybersecurity,” he explains. “People relegate the identity issue to the backburner because they don’t want to do something that’s difficult. It’s a battle getting people to take the identity threat seriously and put some simple things in place.”