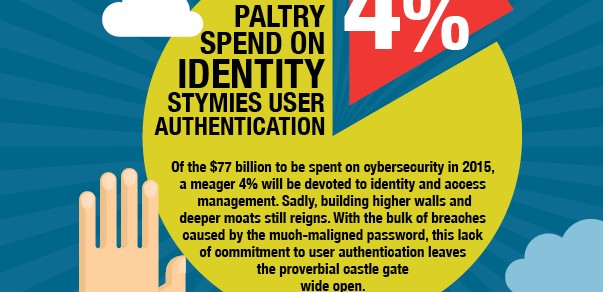
Cybersecurity: Taller walls, deeper moats but the front gate is unguarded
27 July, 2015
category: Corporate, Digital ID, Financial, Government, Smart Cards
The problem with people
The biggest challenge when it comes to online security and identity, however, is the consumer and employee. A CompTIA report found that the biggest factor when it comes to security breaches is people. Some type of formal security training could help mitigate these breaches.
But while training employees and consumers not to click suspicious emails is a step in the right direction, it’s not enough. Better authentication technology is mandatory.
Usernames and passwords remain popular because they’re easy to use. A common word in the strong authentication business these days is friction. It refers to the complexities that are added to a transaction when new authentication is deployed.
“When talking to banks and large consumer-facing web sites, the word friction comes up almost immediately,” says Jim Reno, chief architect for security at CA Technologies. “A tiny increase in friction means a solid drop in service or a significant increase in help desk calls or recovery mechanisms – which drives up cost.”
Google, Apple and others have implemented two-factor authentication as an option but have had limited success, Reno says. “Multi-factor authentication is important but we need to do it while maintaining a user-friendly experience,” he adds.
The mobile is a key piece to this identity puzzle and frictionless authentication, says Gartner’s Ruddy. Instead of issuing hardware tokens enterprises can use a secure app or send a one-time password for multi-factor authentication. “It’s cheaper than hardware tokens and easier to use and implement,” she adds.
Mobile devices have the ability to democratize identity, says Alan Goode, principle at Goode Consulting. “You can’t replace passwords,” he says. “But you can deploy thousands of software tokens to mobile devices and strengthen security overnight.”
Using existing mobile devices is key, Goode explains. “We need to leverage existing authenticators and see them integrate into risk and adaptive security for stronger identity,” he says. “The major authentication platform providers have realized that technology is changing, and there needs to be less emphasis on the authenticator and more emphasis on using risk-based solutions and integrating into threat intelligence.”
Adaptive authentication is another popular term. Adaptive systems use multiple identity attributes to verify an identity – geo-location, biometrics, IP address and others. “The authentication of the future will look like a medical feedback system,” says Ping Identity’s Dingle. “It will be constantly checking for major and minor events and detect a sickness like an EKG detects an arrhythmia.”
Part of the problem is gathering all this data and making it usable. “The idea is to use applications that will take our daily interactions and form a tapestry that can be examined for anomalies or abuse,” Dingle explains.
And the password will most likely still be a part of that tapestry, albeit only one of many threads. “If you look at a bank vault, the combination is just one piece of the security,” Dingle explains. “You don’t put the vault door on the outside of the building. Before you need that combination, you must get past all the guards and cameras.”
Could states crack the digital ID dilemma?
State governments might not be known for taking progressive stances on new technologies but a handful are starting to issue digital identity credentials to citizens for access to government services. While these credentials are initially only used to access one or two sites, other functionality could be added.
Virginia, Michigan, Pennsylvania and North Carolina are issuing digital IDs to citizens for access to Medicaid services. The programs all have a slightly different spin, but in Virginia and North Carolina, the states are leveraging the driver license database to issue higher-assurance credentials.
In North Carolina the credentials are being used to enable access to the state’s Health and Human Services systems, but if the pilot goes well other functions could be added, says Mark DiFraia, senior director of solution strategy at MorphoTrust.
When a person decides to participate in the North Carolina pilot they download an app to their smart device. They scan their driver license, take a selfie and submit that information to be checked through the North Carolina Department of Motor Vehicles, explains DiFraia.
Once a match is made, an eID is tied to the app. When returning to access information on the HHS site they click a different login button and are presented with a QR code. The code is scanned with the app – information is exchanged between the mobile and the site – and access is granted.
The project is in a pilot phase now, but if successful the state plans to allow other relying parties to consume the credential, DiFraia says. “Consumers are aware that they are vulnerable but they don’t know what they can do about it,” he explains. “The average individual doesn’t have something they can run to, so we’re trying to create an electronic ID that’s the same level of trust as the driver license.”
Corporate enterprises are starting to use these systems for employees and they will trickle down for use by consumers, says Kayvan Alikhani, senior director of technology at RSA. The next couple of years will see more uses of advanced technologies. For one, Microsoft’s adoption of fingerprint, iris and face for access and use as authenticators marks a big step. “We’re moving in the right direction but it’s a massive beast and I would say we’re three to five years away from total adoption,” he adds.
Here FIDO, here
Alikhani is referring to Microsoft’s recent adoption of the FIDO Alliance specification for authentication. FIDO standards rely on the existing security of handsets and computers for secure access to other systems.
“FIDO turns credential management upside down,” says Ramesh Kesanupalli, FIDO vice president and founder of Nok Nok Labs. “Instead of generating the private keys on the server side they are generated on the device and the service provider gets the public key back.”
With FIDO a user authenticates to the device and then the device authenticates to the server, Kesanupalli explains. If a service provider is hacked all the fraudster would receive are public keys. In order to get the private key a hacker would have to have access to each specific device. The user would also have the option of choosing the authenticator, be it a built-in fingerprint scanner, facial recognition, voice or a simple PIN.
FIDO has existing deployments enabling the fingerprint scanner on the Samsung Galaxy S5 with PayPal and Alipay. Google is also enabling the FIDO specification for two-factor authentication to Gmail and other accounts. Along with numerous pilots already underway, more relying parties will be deploying uses for FIDO in the coming months, Kesanupalli says.
Business problems
One issue is that some in the identity and access management world have wanted to make money at the cost of good security, says SolPass’ Turissini. “Instead of making this an ecosystem of collaboration, everyone wants to corner the market,” he explains. “Industry needs to embrace a framework and move it forward.”
The payment card market could be an example of how the identity world could work, Turissini says. When the credit card companies federated – decided to all use the same basic infrastructure – it made payments simpler for the retailer and the consumer. “They wanted as many people as possible to come and swipe their credit cards,” he adds.
There are frameworks that identity could borrow from, but there are nuances to identity that make it a bit more difficult. Five years ago if someone found an unauthorized charge on their card they were upset and jumped into action, Galindo says. Now the reaction isn’t as strong, and it can be resolved by simply clicking on a button next to the transaction online.
Identity is harder to resolve because it’s personal. If someone hijacks a Facebook account it’s much more troubling than if an errant charge shows up on a credit card statement.
Identity is forever and along with teaching his children how to ride a bicycle and drive, Galindo also has to teach them to check credit reports and make sure no one has stolen their identities. “We have the usual parental conversations, but now also have to add identity theft and technology use to the list,” he concludes.